[HTB-CyberApocalypse-24] Gloater
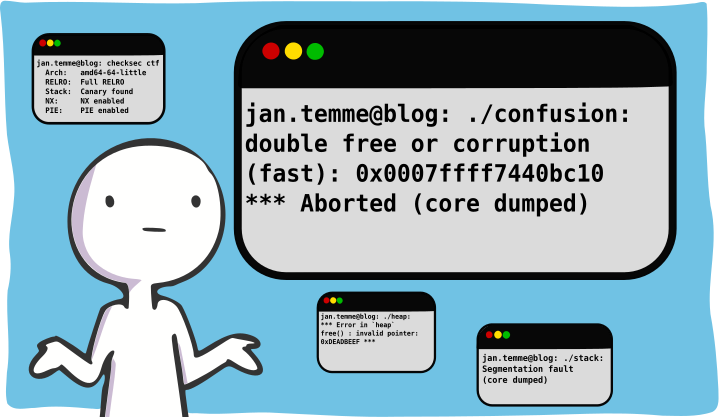
Gloater was a pwn challenge with an insane difficulty rating during the Cyber Apocalypse 2024. While it had the most difficult rating, it wasn't the pwn with the least solves. But it was still an interesting challenge with many options to gain code execution. This writeup certainly presents a ... let's call it special way ;)
Read More